By the Netcomp Solutions Cyber Security Team | Updated May 2026
Picture this: your accounts payable team member gets a call. The voice on the line sounds exactly like your CEO. The caller says it’s urgent, it’s confidential, and they need a payment processed immediately. So your employee complies — and $47,000 disappears.
This isn’t a hypothetical. Consequently, it’s happening to Australian small businesses right now, every single week. And here’s the part that should genuinely concern you: your staff never stood a chance of catching it.
AI-powered phishing has fundamentally changed the threat landscape. Therefore, the old advice — “just look for typos and suspicious links” — is dangerously out of date. This article explains what’s really happening, why Brisbane and Gold Coast businesses are in the firing line, and what actually works to protect your team in 2026.
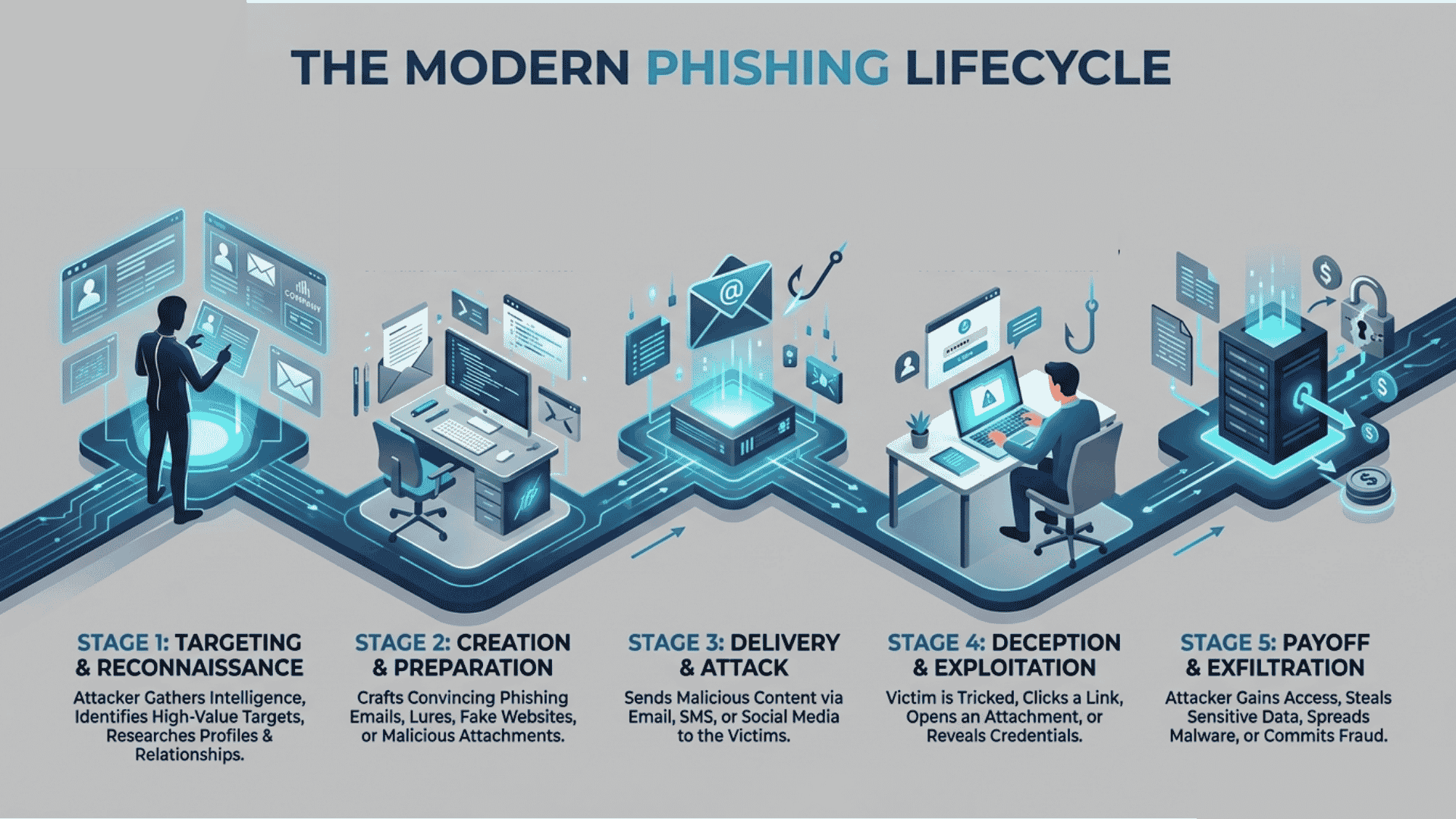
The Death of the Typo: Why “Culturally Accurate Phishing” Is Your New Enemy
Remember when we trained staff to spot dodgy emails because of bad spelling and awkward phrasing? Unfortunately, those days are completely gone.
Today, cybercriminals are using Generative AI to craft phishing emails that are grammatically flawless, professionally formatted, and culturally accurate. In other words, they don’t just sound like English — they sound like your industry, your business, and your clients.
This is what security experts now call culturally accurate phishing. Additionally, it goes far beyond fixing spelling mistakes. AI tools analyse public data about your business — your LinkedIn posts, your website, your social media — and then craft messages that perfectly mimic your internal communication style.
Here’s what culturally accurate phishing looks like in practice for a Brisbane small business:
- An email that appears to come from your accountant, referencing your actual ABN and recent invoice numbers
- A supplier notification that mirrors the exact formatting of your real supplier’s emails
- A “staff policy update” from HR that uses your company’s exact tone and sign-off style
- An ATO notification that looks completely legitimate, right down to correct tax terminology
Furthermore, these emails often arrive at the right time — end of financial quarter, during tax season, or when your team is distracted by a busy period. The timing isn’t accidental; AI tools can identify when Australian businesses are most vulnerable.
The Deepfake Threat: When You Can’t Trust Your Own Ears
Deepfake voice scams in Australia have become the most alarming development in business cybercrime for 2026. Specifically, attackers are now using AI to clone voices from as little as three seconds of audio.
Think about how much audio exists online for most business owners. Your YouTube videos, your podcast appearances, your LinkedIn voice messages — all of it can be used to create a convincing voice clone. Moreover, video deepfakes are now realistic enough to fool employees on video calls.
The scenario playing out across Australia right now:
- Step 1: Attacker researches your business and identifies decision-makers
- Step 2: They scrape audio or video from public sources to clone a voice
- Step 3: They call a finance or admin staff member impersonating the CEO
- Step 4: They create urgency — a deal closing, a confidential acquisition, a tax problem
- Step 5: Staff member processes the transfer before anyone checks
“Australian businesses need to establish out-of-band verification protocols for high-value transactions regardless of how the request arrives.”
Subsequently, no amount of spam filtering will stop a phone call that sounds exactly like your boss. This is why deepfake voice scams are now a standard line item in Australian cyber insurance claims.
The Local Reality: An Australian Business Reports Cybercrime Every 6 Minutes
This is the statistic that should make every Gold Coast and Brisbane business owner sit up straight.
1 report every 6 minutes
The ASD received over 84,700 cybercrime reports in FY2024–25
$56,600 average cost per cybercrime report for small businesses — up 14% year on year
Source: ASD Annual Cyber Threat Report 2024–25
Additionally, that’s the cost per incident — not including the hidden costs of downtime, staff time, reputational damage, and client churn that follow a breach.
Queensland is specifically at elevated risk. The ASD’s own report confirms that Queensland, Victoria and New South Wales continue to report more cybercrime than any other state — with disproportionately higher rates relative to population. Therefore, if you’re operating in Brisbane’s CBD, Fortitude Valley, or along the Gold Coast strip, you’re in one of Australia’s highest-risk cybercrime environments.
Furthermore, that $56,600 figure doesn’t account for the 35% of ransomware victims whose data also gets posted publicly online — triggering Privacy Act notification obligations and potential fines up to $50 million.
The Solution: What Actually Protects Brisbane Businesses in 2026
Here’s where we stop talking about the problem and start talking about what works. Fortunately, effective protection doesn’t require a massive IT budget — it requires the right approach.
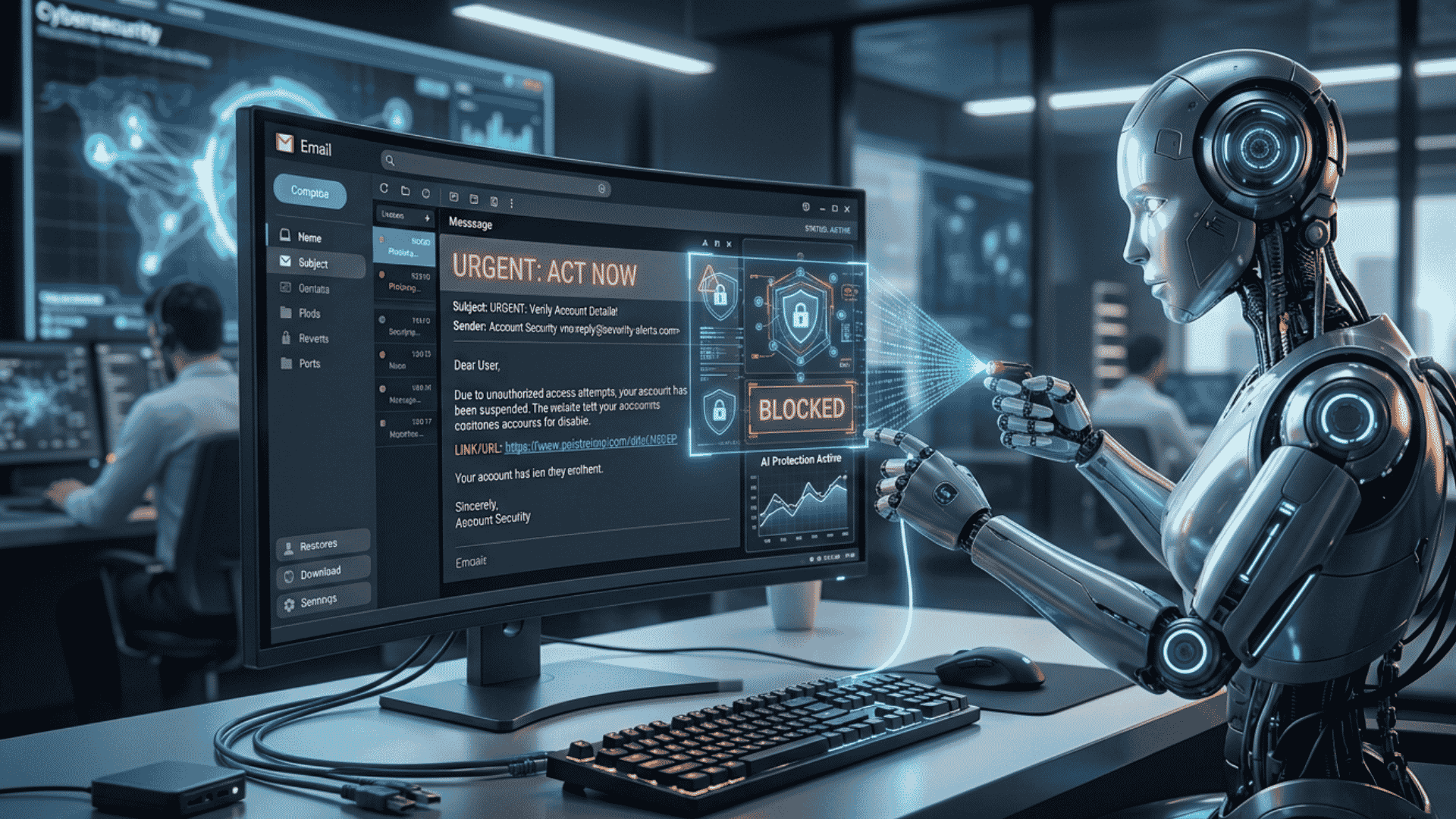
1. Move Beyond SMS MFA to Phishing-Resistant Authentication
Standard SMS-based multi-factor authentication (MFA) was a solid defence in 2020. However, today it’s consistently bypassed by AI-powered attacks through a technique called credential harvesting — attackers use fake login pages to capture your username, password, and SMS code in real time, then replay them immediately.
The 2026 standard for credential harvesting prevention is phishing-resistant MFA, which includes:
- Passkeys — biometric or device-based authentication that cannot be replicated or intercepted
- Hardware security keys (FIDO2/WebAuthn) — physical devices that cryptographically verify you’re on the legitimate website
- Biometric authentication — fingerprint or facial recognition tied directly to your device
Consequently, if your business still relies on SMS codes for email or banking access, moving to phishing-resistant MFA is the single most impactful change you can make today.
2. Essential Eight Compliance: Your Competitive Advantage in Queensland
Many Gold Coast businesses view the ASD’s Essential Eight framework as a compliance checkbox. However, the smart ones are using it as a competitive advantage.
Organisations supplying services to the Queensland Government are required to demonstrate compliance with the Queensland Government Information Security Policy (IS18), which directly references the Essential Eight. Failing to meet this can mean losing government contracts entirely.
Additionally, beyond government contracts, Essential Eight compliance QLD is now required by:
- Cyber insurers — who treat it as a minimum underwriting standard in 2026
- Supply chain partners — larger businesses auditing vendors for security posture
- Healthcare and professional services clients — who need to demonstrate data protection to their own regulators
For most Brisbane and Gold Coast SMBs, achieving Maturity Level 1 across all eight controls is the immediate priority. Furthermore, a clear roadmap to Level 2 over 12 months puts you ahead of the majority of competitors who haven’t started.
⚠️ Important: Your overall Essential Eight maturity level is determined by your lowest-scoring control. Therefore, being excellent in seven areas but ignoring one means attackers will find that gap — and exploit it.
Learn more: ASD Essential Eight Framework — cyber.gov.au
3. Human Risk Management: Why Annual Training Is Dead
Here’s an uncomfortable truth most IT companies won’t tell you: the annual “cybersecurity awareness” session your staff do every December is essentially useless against 2026 threats.
“One in three breaches in 2026 still start with a staff mistake — such as clicking a malicious link.”
However, the problem isn’t that your staff are careless. Instead, it’s that one-off training doesn’t build reflexes — it builds temporary awareness that fades within weeks. Furthermore, it doesn’t prepare staff for AI-generated phishing emails that look completely legitimate.
The 2026 standard for Human Risk Management includes:
- Real-time phishing simulations — regular, unannounced test emails sent to staff throughout the year
- Immediate micro-training — when a staff member fails a simulation, they receive instant, relevant training (not a lecture months later)
- Role-based training — your finance team faces different threats than your receptionist; consequently, their training should reflect that
- Deepfake and voice scam scenarios — training that specifically covers how to verify urgent requests via a second independent channel
Additionally, every staff member needs a clear, simple protocol for verifying unexpected requests — especially anything involving payments or access changes. Therefore, the rule is straightforward: if you receive an urgent financial request by any channel, verify it through a completely separate channel before acting.
What Managed IT Services in Brisbane Should Be Doing For You
If your current Managed IT Services Brisbane provider hasn’t raised any of the above with you, that’s a red flag worth paying attention to.
Effective managed IT support in 2026 isn’t just about fixing computers when they break. Specifically, it means proactively managing your cyber risk, keeping your Essential Eight controls current, running phishing simulations, and helping you respond when — not if — an incident occurs.
At Netcomp Solutions, we work specifically with Brisbane and Gold Coast small businesses to implement exactly this kind of layered, practical protection. Moreover, we don’t believe in selling complexity — we believe in making security manageable for real businesses with real budgets.
Here’s what a strong cyber security partnership looks like:
- ✅ Regular Essential Eight assessments — knowing your maturity level and improving it over time
- ✅ Phishing-resistant MFA deployment — moving your team off SMS codes to safer authentication
- ✅ Ongoing phishing simulations — building genuine awareness through practice, not lectures
- ✅ Clear incident response plans — so you know exactly what to do when something happens
- ✅ Deepfake verification protocols — simple rules that stop voice scams before they start
Your Next Step: A Free Cyber Security Assessment
The threat is real. Additionally, the cost of doing nothing — measured at $56,600 per incident for the average Australian small business — is far higher than the cost of getting it right.
If you’re a Brisbane or Gold Coast business owner who’s not confident your current defences would stop an AI-generated phishing attack, we’d like to help.
Get a no-obligation Cyber Security Assessment
We’ll review your setup against the Essential Eight, identify your risk areas, and give you a clear roadmap — no jargon.Book Your Free Assessment → netcomp.com.au
Because the best time to fix your security was before the attack. However, the second-best time is right now.
Sources & Further Reading
- ASD Annual Cyber Threat Report 2024–25 — Australian Signals Directorate (cyber.gov.au)
- ASD Essential Eight Framework — cyber.gov.au
- AI Cybersecurity: Australia’s Growing Threat Landscape 2026 — Cyble Research
- AI Cybersecurity in 2026: The Threat Landscape Australian Businesses Face — ValiDATA
- 2025 in Cyber: The Threats That Changed the Landscape — Interactive Australia
Netcomp Solutions provides Managed IT Services and cyber security for small businesses across Brisbane, the Gold Coast, and South East Queensland. Visit netcomp.com.au or call our team to learn how we can protect your business.