Updated: April 2026 | Reading time: ~8 minutes
Cyberattacks are hitting Australian small businesses harder than ever before. Consequently, the way you protect your accounts in 2026 looks very different from just a few years ago. Therefore, if you rely on passwords alone, your business is already at risk.
This guide covers everything you need to know about multi-factor authentication (MFA) for Australian businesses — what it is, why basic MFA is no longer enough, and how to implement the right solution today.

So, what is Multi-Factor Authentication?
Simply put, multi-factor authentication is a security method that requires more than one form of verification. Instead of relying solely on a password, MFA adds an extra layer — such as an app approval, fingerprint, or hardware key.
However, MFA has evolved significantly since 2023. Furthermore, the threats it protects against have become far more sophisticated. Accordingly, the Australian Signals Directorate (ASD) now recommends phishing-resistant MFA as the gold standard for all businesses.
Why Australian Businesses Can’t Ignore MFA in 2026

The numbers paint a clear picture. Specifically, the ACSC Annual Cyber Threat Report recorded 87,400 cybercrime reports in the 2023–24 financial year — roughly one every six minutes.
Moreover, credential theft surged by 160% in 2025 and now accounts for one in five data breaches globally. Additionally, the average cost of a cyber incident for an Australian small business now exceeds $46,000 — and 60% of small businesses never recover from a serious breach.
Real Australian Breaches Caused by Missing MFA
These aren’t just statistics — they represent real businesses. Notably, two high-profile examples show exactly what’s at stake:
- Medibank (2022): Attackers accessed VPN accounts using stolen contractor credentials. Critically, MFA was not enforced on those accounts. As a result, 9.7 million customer records were stolen and hundreds of millions were spent on remediation.
- Australian Superannuation Funds (2025): Criminals used credential-stuffing attacks against AustralianSuper, Hostplus, and Rest. Consequently, hundreds of thousands of dollars were stolen before the attack was detected. Weak SMS-based MFA could not withstand the automated attack scale.
The pattern is consistent: stolen passwords plus absent or weak MFA equals a catastrophic breach.
MFA in 2026: It’s Not the Same as Before

This is the critical point that many businesses miss. Specifically, basic MFA methods — like SMS text codes — are no longer considered safe enough for most business scenarios.
Why SMS-Based MFA Is No Longer Sufficient
Attackers have developed sophisticated ways to bypass traditional MFA. For instance:
- SIM-swapping allows criminals to redirect your SMS codes to their device.
- Real-time phishing kits intercept one-time codes before they expire.
- Session token theft can bypass MFA entirely after login — research shows 79% of business email compromise victims in 2024–25 had MFA correctly set up yet were still breached this way.
Therefore, SMS should only be used as a last resort, not as your primary MFA method.
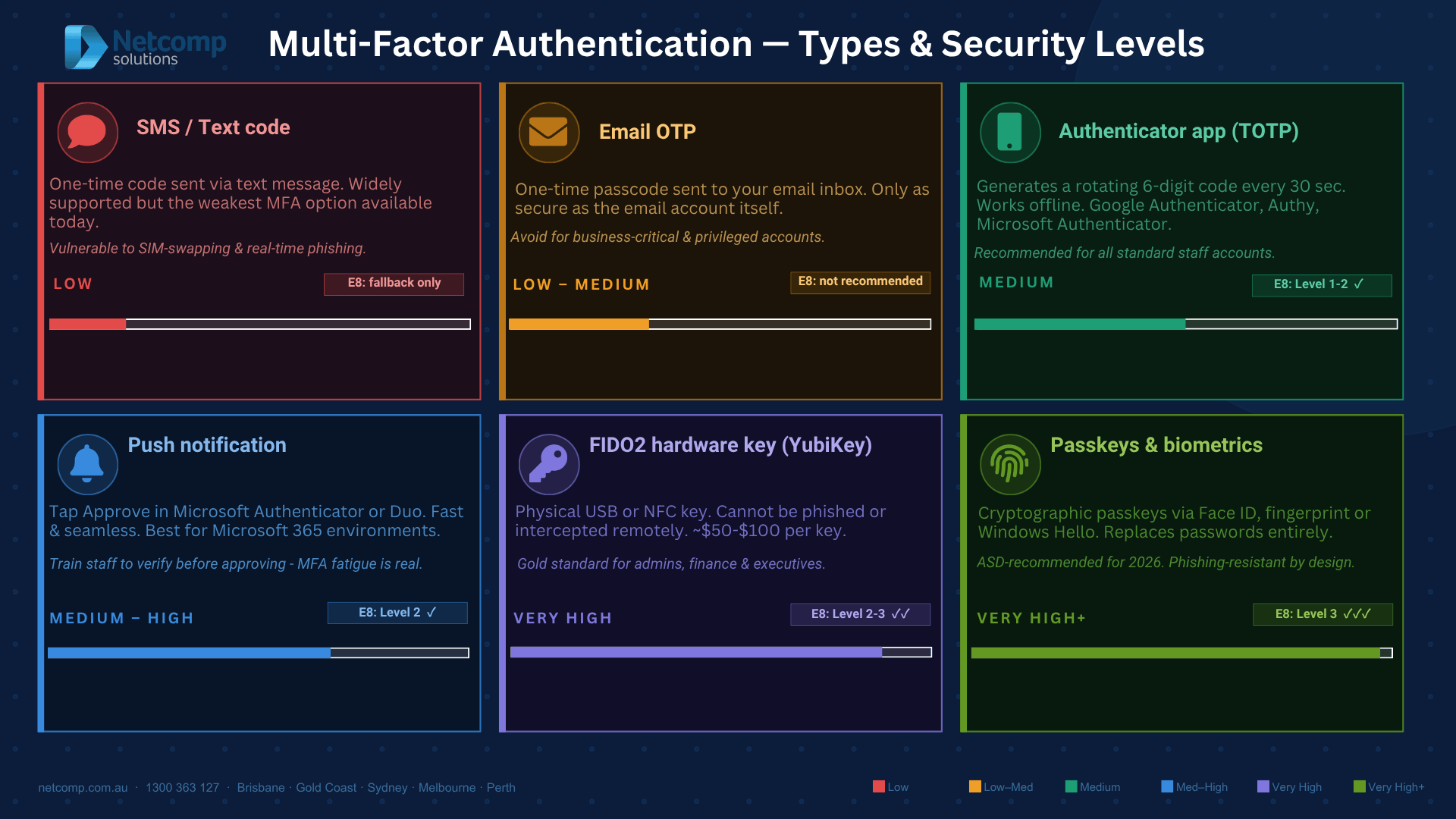
What Counts as Strong MFA in 2026
The Australian Cyber Security Centre now recommends phishing-resistant MFA wherever possible. Specifically, this means:
| MFA Type | Security Level | Best For |
|---|---|---|
| SMS / Text Code | Low (avoid if possible) | Legacy fallback only |
| Email OTP | Low | Legacy fallback only |
| Authenticator App (TOTP) | Medium | Most staff accounts |
| Push Notification (e.g. Microsoft Authenticator) | Medium-High | Office 365 / Microsoft 365 users |
| FIDO2 Hardware Key (e.g. YubiKey) | Very High | Admins, finance, executives |
| Passkeys / Biometrics | Very High | Modern cloud platforms |
MFA and Australia’s Essential Eight Framework
If your business works with government clients, handles sensitive data, or operates in a regulated industry, you need to understand the Essential Eight framework. Essentially, MFA is one of the eight core cybersecurity strategies mandated by the ASD.
What Each Maturity Level Requires for MFA
- Maturity Level 1 (Minimum baseline): MFA applied to remote access and internet-facing services.
- Maturity Level 2 (Recommended for most businesses): MFA enforced across all users, cloud services, and privileged accounts. Importantly, phishing-resistant MFA is required for admin users at this level.
- Maturity Level 3 (High-risk sectors): Phishing-resistant MFA for all access — SMS authentication is explicitly insufficient at this level.
Critically, by 2026, most Australian businesses should be targeting Maturity Level 2 as a minimum. In fact, most government agencies are required to reach Level 2 or higher.
MFA for Microsoft 365: The Most Common Setup for Australian SMBs
Most Australian small businesses use Microsoft 365 for email, Teams, and document management. Fortunately, setting up MFA here is straightforward.
Importantly, Microsoft now mandates MFA for the Microsoft 365 Admin Centre as of February 2026. Therefore, if you manage a Microsoft 365 environment, this is no longer optional.
Your Four MFA Options for Microsoft 365
1. Microsoft Authenticator App (Recommended)
Download the free app from the Apple App Store or Google Play. Next, add your account, scan the QR code on screen, and you’re protected. Push notifications make approving logins quick and seamless.
2. Authenticator TOTP Code
Alternatively, use any TOTP app (like Google Authenticator or Authy) to generate a rotating 6-digit code. This is a solid option for staff who prefer not to receive push notifications.
3. SMS Text Code
While still supported, SMS is increasingly discouraged for business accounts. However, it remains a useful fallback for staff without smartphones.
4. FIDO2 Hardware Security Key (e.g. YubiKey)
This is the gold standard for your highest-risk accounts — admins, finance, and executives. Additionally, hardware keys work for businesses that want to avoid using personal phones for authentication altogether.
What About Passkeys?
Passkeys are an emerging alternative to both passwords and traditional MFA. Instead of combining a password with a second factor, passkeys use a single cryptographic credential stored on your device.
Consequently, passkeys are phishing-resistant by design because they are tied to the exact domain you’re logging into. Furthermore, major platforms including Microsoft, Google, and Apple now support passkeys natively. As a result, the ASD specifically recommends passkeys as a preferred option for 2026 onwards.
Protecting Against Modern MFA Bypass Attacks
Even with MFA in place, additional controls are essential. Specifically, consider these measures to close common gaps:
Conditional Access Policies
Tools like Microsoft Entra ID let you restrict logins to registered, compliant devices. Therefore, even if credentials and MFA codes are stolen, attackers cannot log in from an unrecognised device.
Short Session Timeouts
Importantly, set sessions to expire after a reasonable period. Consequently, stolen session tokens become useless quickly.
Zero Trust Architecture
Rather than trusting a user once they log in, Zero Trust continuously verifies every session. Furthermore, this approach significantly limits the damage if one account is compromised. Learn more about our Cybersecurity services to explore Zero Trust options.
How to Roll Out MFA Across Your Business: A Simple Plan
Rolling out MFA doesn’t have to be disruptive. Instead, follow this practical sequence:
Step 1 — Start with your highest-risk accounts
Begin with admins, executives, and finance staff. Critically, these accounts carry the most damage potential if compromised.
Step 2 — Choose the right MFA method
Use authenticator apps as your standard. Subsequently, add hardware keys for your most sensitive accounts.
Step 3 — Enable MFA across all cloud services
This includes Microsoft 365, your accounting software, your CRM, and any remote access tools. Essentially, if it’s internet-facing, it needs MFA.
Step 4 — Train your team
Briefly explain why MFA matters and how to use it. Additionally, warn staff about MFA fatigue attacks — where attackers spam approval requests hoping someone clicks “Allow” by mistake. Our Cybersecurity Training program covers this in detail.
Step 5 — Review and audit regularly
Periodically, check that MFA is enforced for all accounts. Furthermore, remove MFA access for departed staff immediately. Consider a Cybersecurity Audit to confirm everything is properly configured.
MFA and Cyber Insurance
Increasingly, Australian cyber insurers are requiring MFA as a condition of coverage. Specifically, many policies now exclude breaches where MFA was available but not enabled. Therefore, implementing strong MFA also protects your ability to make a claim if something goes wrong.
Frequently Asked Questions
Is MFA enough to protect my business?
MFA is the single most effective first step, but it works best alongside other controls like email security, endpoint protection, and regular backups. Consequently, we recommend treating it as part of a layered security strategy rather than a standalone solution. Explore our full Cybersecurity services to see how these layers work together.
Does MFA work for remote employees?
Absolutely — in fact, MFA is especially critical for remote access. Additionally, combining MFA with a VPN and Conditional Access policies provides the most robust remote work security. Our Remote IT Support team can help configure this correctly.
How much does MFA cost?
For Microsoft 365 users, the Microsoft Authenticator app is free. Furthermore, most Microsoft 365 business plans include MFA capabilities at no extra cost. Hardware keys like YubiKey typically cost between $50–$100 per user — a fraction of the $46,000+ average cost of a breach.
What if my staff resist using MFA?
Modern MFA, particularly push notifications, adds only a few seconds to the login process. Moreover, once staff understand the real consequences of a breach, adoption improves significantly. Our IT Support team regularly assists businesses through this change management process.
The Bottom Line: MFA Is Non-Negotiable in 2026
Passwords alone will not protect your Australian business. Furthermore, basic SMS codes are no longer reliable against modern attacks. Therefore, implementing phishing-resistant MFA — combined with Conditional Access policies and regular staff training — is the most effective step you can take right now.
The ACSC recommends strong MFA as the number-one action for all Australian businesses. Additionally, your cyber insurer likely requires it. Most importantly, your business data and your customers depend on it.
Ready to implement MFA or review your current setup? Contact the Netcomp team for a straightforward, step-by-step implementation guide tailored to your business.
You can also explore our Cybersecurity Audit, Endpoint Protection, Email Security, and IT Compliance services to build a complete security posture for 2026.
Serving businesses across Brisbane, Gold Coast, Sydney, Melbourne, and Perth.